8 Email Attacks That Bypass Microsoft Defender for Office 365 in 2026
In October 2025, Microsoft Defender for Office 365 blocked more than 13 million emails linked to the Tycoon2FA phishing-as-a-service platform. In a single month. That figure comes directly from Microsoft's own threat intelligence blog published January 6, 2026.
I spent years at FireEye building advanced threat detection systems. That number does not shock me. What it communicates — and what every CISO running Microsoft 365 should take from it — is not that Defender is failing. It is that the scale and sophistication of email attacks against Microsoft 365 environments has reached a level that makes the gaps in native detection more consequential every month.
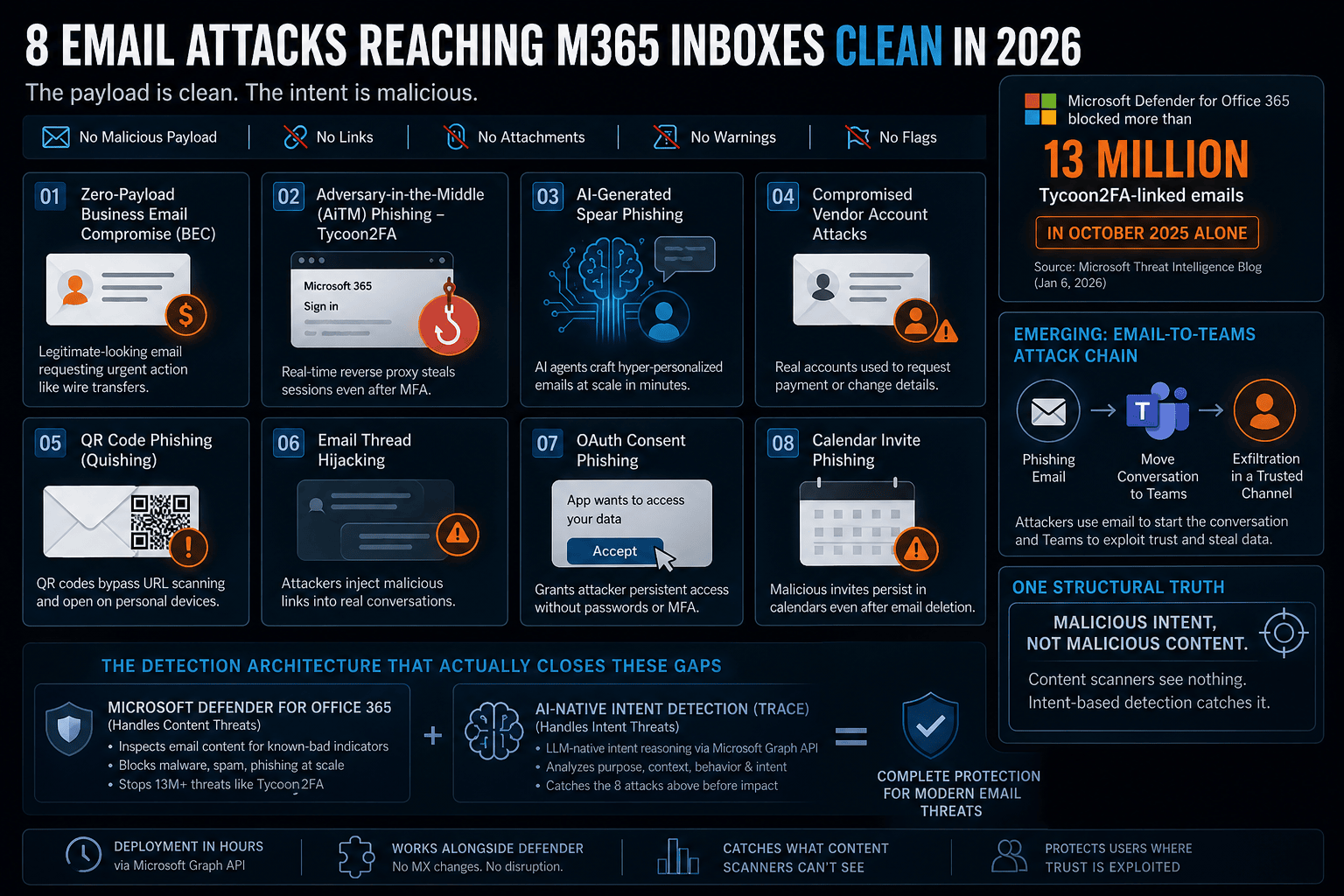
Because for every Tycoon2FA email Defender caught, the platform was simultaneously running active campaigns. And the eight attack types below are the ones that land in inboxes clean — logged by Exchange Online Protection and Defender as no threat detected, delivered without a flag, without a warning banner, without any indication that the most consequential email of the quarter just arrived.
This is not a criticism of Microsoft. Defender is doing exactly what it was designed to do: inspect email content for known-bad indicators. Every attack on this list was engineered around a single insight — if there is nothing malicious in the content, a content scanner finds nothing malicious. The malice is in the intent of each email, not its payload. Detecting intent requires a different architecture entirely.
Here are the eight attack types reaching Microsoft 365 inboxes clean in 2026 — what they look like in practice, precisely why Defender misses each one, and what detection architecture actually catches them.
Defender's model answers one question: does this email contain something we have seen before? Every attack on this list was designed to answer that question with: no, it does not. The malice is in purpose, not payload.
01 Zero-Payload Business Email Compromise (BEC)
It is Thursday, 4:47 PM. A finance director at a 700-person professional services firm is working through her inbox before a weekly review. An email arrives appearing to come from the firm's managing partner — his correct name, his real email address format, his signature communication style. He is referencing a client matter she has been working on for weeks and asking her to process an expedited wire transfer to a new escrow account before close of business. The deadline is real. The client matter is real. The managing partner's email address is not.
The sender domain is four days old. It has never sent email before — malicious or otherwise. The message contains no link, no attachment, no embedded image, no suspicious formatting of any kind. Exchange Online Protection checks the domain: no reputation. Defender's anti-phishing policies check for impersonation against the firm's protected domains: clean — this is not impersonating a protected domain, it is using a lookalike domain that no policy has been written for. Every check passes. The email is delivered with no warning.
The FBI's 2024 Internet Crime Report documents $2.77 billion in Business Email Compromise losses across 21,442 reported incidents — a 37 percent year-over-year increase. Verizon's 2025 DBIR identifies social engineering, which encompasses BEC, as producing the highest financial loss per incident of any attack category. Every dollar of that loss flows through an email that security platforms logged as clean.
BEC works because it exploits a structural limitation that applies to every content-inspection architecture: you cannot detect intent by scanning payload. A fraudulent wire transfer request is indistinguishable from a legitimate one at the content layer. The malice is not in the email — it is in what it is trying to make happen. Catching it requires evaluating what action is being engineered, whether the urgency is artificial, whether this sender-recipient pair has ever had this type of financial exchange, and whether the requested action bypasses the firm's normal approval controls. These are questions a skilled analyst asks. They are also the questions that LLM-native intent reasoning was designed to answer at machine speed.
WHY DEFENDER MISSES IT: No malicious payload, URL, or attachment. New sender domain with zero prior history — no reputation signal to flag. Anti-phishing impersonation policies only protect explicitly listed domains. Every EOP and Defender check finds nothing because there is nothing in the content to find.
WHAT CATCHES IT: LLM-native intent reasoning: evaluating the purpose of the request, the consistency of that request with the sender-recipient relationship history, the artificial urgency framing, and whether the action being requested — an urgent off-process wire transfer — is consistent with how this managing partner has communicated in the past.
02 Adversary-in-the-Middle (AiTM) Phishing — Tycoon2FA and the PhaaS Ecosystem
A senior account manager at a financial services firm receives a Microsoft security notification: her session has expired on multiple devices and she needs to re-verify her identity before accessing a set of client documents she needs for a morning meeting. The link resolves to what is visually, functionally, and technically identical to the Microsoft 365 sign-in page — because it is. A real-time reverse proxy is pulling the genuine Microsoft authentication interface and serving it through attacker-controlled infrastructure. She enters her credentials. Her Microsoft Authenticator app receives a push notification, which she approves. She is redirected to her inbox. Within 90 seconds, the attacker holds her authenticated session cookie, has access to her mailbox, calendar, OneDrive, and SharePoint, and her account will show no anomalous sign-in — because the authentication was completed correctly, by her, against the real Microsoft system.
Standard multi-factor authentication does not protect against this. The user completed a genuine MFA challenge. What the attacker captured was the session token issued after successful authentication — not the credential, not the MFA code. Resetting the password does not invalidate an active session token. The attacker maintains access until the token expires or is explicitly revoked from the Entra ID session management console.
Microsoft's own threat intelligence team confirmed that Defender blocked more than 13 million Tycoon2FA-linked emails in October 2025 alone. Tycoon2FA is the dominant AiTM phishing platform targeting Microsoft 365 — available to threat actors for less than $100 per month, with no technical expertise required. It automates infrastructure provisioning, real-time proxying of Microsoft authentication pages, session token capture, and credential storage. The barrier to running a sophisticated AiTM campaign is now a credit card and 20 minutes of setup.
The detection gap is precise. Tycoon2FA campaigns rotate infrastructure continuously. The phishing URL in the email points to newly provisioned proxy infrastructure with no prior malicious reputation at delivery time. Defender's Safe Links checks the URL on delivery and rewrites it. At click time, if the infrastructure has since been flagged, the user sees a warning. But if the URL is first-used against this organisation, both the delivery check and the click-time check return clean results. The first organisation that clicks it is also the first data point the reputation system receives.
WHY DEFENDER MISSES IT: AiTM infrastructure is continuously rotated — the phishing URL has no prior malicious reputation at delivery or click time. Safe Links evaluates at both points and finds nothing to flag. The MFA challenge the user completes is entirely genuine against the real Microsoft system.
WHAT CATCHES IT: Pre-click detection at the email layer: recognising the manufactured authentication urgency, the structural characteristics of credential phishing independent of URL reputation, and the misalignment between the claimed sender identity and the infrastructure behind the link — before the session is ever touched.
03 AI-Generated Spear Phishing — Precision at Industrial Scale
The morning after a company's Q1 earnings call, a senior sales director receives an email. It references a specific customer deal she mentioned during her presentation — by name, with the correct approximate deal size. It uses her preferred nickname, which appears in her LinkedIn profile but not in her email signature. It arrives at 8:09 AM, before her first scheduled meeting. It asks her to review a contract addendum before a 9:30 AM client call. The link goes to what appears to be a Microsoft SharePoint document library.
Three years ago, this level of personalisation would have taken a skilled attacker several hours to research and write. In 2026, an autonomous AI agent can produce it in under four minutes — scraping the earnings call transcript, her LinkedIn profile, public press releases referencing the client deal, and any prior public content that reveals her communication preferences. The agent sets the objective. The research, writing, personalisation, and sending are fully automated.
What makes AI-generated spear phishing structurally different from bulk phishing at the detection layer is that every message is unique. There is no template. No shared URL structure. No common sending infrastructure across the campaign. A finance controller, a legal associate, and a sales director at the same company might all receive targeted phishing on the same morning — and each email would be substantively different in content, framing, and the specific business references it exploits. Signature-based detection needs something to match against. AI-generated attacks produce nothing to match, because every attack is generated fresh for its specific target.
IBM's 2025 Cost of Data Breach Report confirms phishing as the most expensive initial attack vector at $4.8 million average breach cost. The FBI's 2024 IC3 Report identifies AI-assisted phishing as the primary driver of the 37 percent year-over-year BEC increase. These are outcomes from attacks that passed every content-inspection layer cleanly — not because those layers failed, but because the attacks were never designed to produce a detectable signal at the content layer.
WHY DEFENDER MISSES IT: Every AI-generated spear phishing email is structurally unique — no template match, no shared URL infrastructure, no prior campaign data to catalogue. Grammatically flawless, contextually accurate, timed precisely. There is nothing in Defender's detection model that applies to a message it has never seen in any form.
WHAT CATCHES IT: Semantic analysis of the email's purpose: identifying the engineered personalisation structure, the artificial deadline framing, and the logical architecture of a social engineering attempt — regardless of the specific words, references, or business context used.
04 Compromised Vendor Account Attacks — Trust Borrowed, Purpose Stolen
A manufacturing company's accounts payable coordinator has exchanged 71 emails with a logistics vendor over 26 months. Invoices, delivery confirmations, occasional scheduling notes. The relationship is completely unremarkable. On a Tuesday morning she receives what appears to be email 72: a routine follow-up to an outstanding invoice, with a brief note that the vendor has updated their banking details following a recent internal restructure and asking that the next payment go to the new account. Attached is a clean PDF — a payment instruction form.
The vendor's Microsoft 365 account was compromised 23 days earlier. The attacker spent those 23 days in silent reconnaissance: reading every email, learning the communication style, identifying which invoices were outstanding, noting which AP contacts had authority over payments, and selecting the precise moment to intercept. The PDF contains no malicious code — it is a genuinely clean document with a fraudulent bank account number. The only thing wrong with email 72 is its purpose.
Defender checks the sender domain: clean — three years of legitimate sending history. Checks the sender address: clean — this address has exchanged dozens of legitimate messages with this exact recipient. Checks the attachment: a standard PDF with no embedded scripts. Anti-phishing impersonation policies: not triggered — this is the real sender address from the real domain, not an impersonation. Every single check passes. The compromise happened at the vendor's environment, not the target's. Defender has zero visibility into external account takeover.
What Defender cannot know — because no reputation system or content scanner can know — is that this sender has sent 71 emails and never once included a request to change banking details. That deviation from 26 months of established relationship history is the signal. It exists nowhere in a threat feed or blocklist. It exists only in the behavioral record of this specific sender-recipient relationship, and detecting it requires maintaining that record and reasoning about it.
WHY DEFENDER MISSES IT: Legitimate domain with years of clean sending history. Real sender email address. Clean PDF attachment with no malicious code. The compromise is upstream at the vendor's environment — entirely outside Defender's visibility.
WHAT CATCHES IT: Individual sender-recipient behavioural baseline: 71 messages in 26 months with zero payment redirection requests. The introduction of bank account change instructions in message 72 is a statistically anomalous deviation that intent-based reasoning detects from relationship context alone.
05 QR Code Phishing (Quishing) — No URL, No Scan, No Warning
An operations manager receives what appears to be a Microsoft Authenticator update notification from IT. His organisation has been rolling out new MFA policies and this is the third security-related communication from IT this week. The email is formatted correctly, references the right policy rollout, and contains a single instruction: scan the QR code below with your mobile device to complete the security update. He scans it on his iPhone. His mobile browser opens to a Microsoft 365 credential harvesting page. He enters his password and approves the MFA prompt. His credentials are compromised — on a personal device, on a home network, through a camera app, completely outside every security control his organisation has deployed.
QR code phishing defeats two independent protection layers simultaneously. First, it defeats Safe Links: there is no URL in the email body for Safe Links to scan or rewrite. The malicious destination is encoded inside an image — a format that Defender's URL inspection has no mechanism to process. Second, it defeats corporate web filtering and endpoint security: the link is opened by the mobile camera app on an unmanaged personal device, on a network outside the corporate proxy. No EDR. No conditional access policy requiring a compliant device. The entire credential harvest occurs in a blind spot that exists by design in the intersection of personal device usage and corporate security architecture.
CISA and the FBI both issued alerts in 2024 and 2025 specifically about QR phishing campaigns targeting Microsoft 365 environments. The attack is particularly effective against organisations that have invested in MFA — because those organisations have specifically trained employees to expect QR codes as a legitimate authentication mechanism. The trust being exploited was built by the security programme itself.
Microsoft's own Defender documentation acknowledges this gap explicitly: 'Safe Links does not block calendar invites from being delivered... Consideration: Safe Links only inspects clickable URLs and does not protect against QR codes.' The same limitation applies to QR codes in email bodies.
WHY DEFENDER MISSES IT: No URL in the email body for Safe Links to process. The malicious destination is encoded in an image. Interaction happens on a personal mobile device outside the corporate security perimeter — entirely beyond Defender's architectural reach.
WHAT CATCHES IT: QR code payload extraction and destination analysis before delivery: decoding embedded QR codes, evaluating the destination against the email's claimed purpose, and identifying the combination of IT impersonation framing and QR-based credential collection as a social engineering attack pattern.
06 Email Thread Hijacking — Injecting Malice into Real Conversations
A procurement manager had a straightforward email exchange with an external consultant four weeks ago about project deliverables. The thread ended naturally. Today she receives what appears to be the consultant following up: the correct 'Re:' subject line, the full original thread quoted below, and a brief message asking her to review an updated project charter before next week's milestone review. The link is to what appears to be a Microsoft SharePoint folder.
The consultant's email account was compromised. The attacker accessed the original thread, read the context, understood the relationship and the project, waited for an opportune moment, and injected a single malicious message into an otherwise legitimate conversation. The email arrives carrying the full legitimacy of an established ongoing business relationship. The recipient has no reason for suspicion — she remembers this thread, she knows this consultant, and the request is contextually plausible.
From Defender's perspective this attack offers almost nothing to flag. The sending domain is legitimate — the consultant's real domain. The sender email address is known and has sent legitimate mail before. The phishing URL may be newly provisioned with no reputation history. Even if it is flagged by Safe Links, the established trust of the thread context dramatically reduces the user's likelihood of heeding a warning — a documented pattern in social engineering research showing that contextual trust overrides technical alerts for most users in real working conditions.
Thread hijacking is particularly damaging in accounts payable, legal, and procurement workflows — roles that regularly correspond with external parties about financial and contractual matters. The trust was built legitimately over months or years. The attacker borrows it with a single message.
WHY DEFENDER MISSES IT: Legitimate sending domain and email address with an established trust history. Real prior thread context. The phishing URL may have no reputation — but even when flagged by Safe Links, the established relationship context undermines the warning's impact.
WHAT CATCHES IT: Anomaly detection at the individual sender-recipient level: identifying that this sender has never previously shared a document via this platform in all prior messages, that the communication pattern of this specific message deviates from the established conversational rhythm, and that the request introduces a new external link without the contextual justification that would be present in a legitimate continuation.
07 OAuth Consent Phishing — Persistent Access Without Credentials or MFA
A legal associate at a law firm receives an email appearing to come from Microsoft, informing him that the firm's IT team has deployed a new document collaboration integration for Microsoft 365. He clicks the link. He is presented with a standard Microsoft OAuth consent screen — the same interface he has seen when authorising legitimate integrations like Docusign, Adobe Sign, or the firm's legal research platform. The consent screen lists the permissions being requested: read access to email, calendar, and OneDrive files. He clicks Accept. The consent screen closes and he is redirected to what appears to be the integration's welcome page.
He never entered his password. He never received an MFA challenge. He has just granted an attacker-controlled application persistent, delegated API access to his entire Microsoft 365 account — access that will survive password resets, MFA re-enrolment, and even account lockouts, because it was granted through the application permission model, not the authentication model. Revoking it requires identifying and removing the malicious application from the firm's Entra ID app registrations — an action that requires admin privileges, knowledge of where to look, and typically does not happen until the breach is discovered weeks or months later.
Microsoft's own Security Blog, published March 2, 2026, documented active OAuth redirection abuse campaigns targeting government and public-sector organisations, noting that attackers 'combined trusted authentication URLs with collaboration-themed lures' and used fake calendar invite (.ics) attachments to reinforce legitimacy. The technique works because the entire consent flow happens on legitimate Microsoft infrastructure — the email links to login.microsoftonline.com, the consent screen is the genuine Microsoft OAuth interface, and the user is making a real permission grant through a real Microsoft system. There is nothing technically malicious for Defender to detect.
The attack also requires no prior credential compromise and produces no anomalous authentication event. From an audit log perspective, the attacker's access looks like an authorised application accessing the mailbox on the user's behalf — which is exactly what it is. Standard SIEM alerts for impossible travel, unfamiliar sign-in location, or anomalous authentication do not fire. The access is invisible until someone audits the tenant's third-party application consent grants.
WHY DEFENDER MISSES IT: The email links to a legitimate Microsoft authentication domain. The consent flow occurs on genuine Microsoft infrastructure. No malicious payload, no malicious URL, no anomalous authentication event. The threat exists entirely in the OAuth application being authorised — outside email security scope.
WHAT CATCHES IT: Intent analysis of what the email is engineering the user to do: identifying that the action being requested — granting third-party application permissions — is inconsistent with legitimate IT deployment communication patterns, and that the social engineering framing specifically mimics IT notification language to reduce scrutiny of an unusual request.
08 Calendar Invite Phishing — The Attack That Survives Email Deletion
A finance manager receives a meeting invitation appearing to come from a partner organisation she has been collaborating with. The invitation is for a Q2 planning sync — contextually plausible, professionally formatted, with an agenda and a video call link in the location field. She clicks Accept in her Outlook calendar pane. The meeting is now on her calendar. Three days later, working from home with her inbox closed, she notices the event on her phone's calendar and clicks the video link to join. The link goes to a credential harvesting page.
The email containing the invitation was deleted from her inbox two days ago — flagged by her SOC team and remediated. But the calendar event was not deleted. And this is the architectural characteristic that makes calendar invite phishing uniquely dangerous: Outlook automatically creates a calendar entry during email delivery, storing it separately from the email itself. When the email is deleted — even by a SOC team using Defender's remediation tools — the calendar entry persists. The attack survives its own remediation.
Microsoft recognised this gap and shipped a product update in November 2025: Defender's Hard Delete action now also removes the associated calendar entry when removing a meeting invite email. Help Net Security documented the update directly, noting that 'meeting invite emails introduce an additional challenge — even after the email is removed, Outlook automatically creates a calendar entry during delivery, which remains accessible to users.' However, Microsoft's own documentation confirms that this remediation does not apply to calendar entries added via .ics file attachments — a delivery method commonly used in phishing campaigns to bypass mail flow rules. The gap is partially closed but not fully.
The attack surface extends further. Malicious links can be embedded in the Location field of calendar invites — a field that most users never scrutinise but that Outlook renders as a clickable element. Research published in March 2026 documented a campaign combining .ics attachments with QR codes inside the calendar event: simply previewing the .ics attachment in Outlook was sufficient to add the malicious calendar entry, without the file ever being downloaded. A follow-up invite was automatically sent after the first interaction, indicating infrastructure designed for persistent re-engagement.
Microsoft's Defender documentation is explicit about Safe Links' limitations here: Safe Links does not protect against QR codes embedded in calendar events. The attacker exploits the trust users place in calendar notifications — a context where security awareness is lower, urgency is implied by the scheduled nature of meetings, and the interaction happens from mobile devices where security controls are thinner.
WHY DEFENDER MISSES IT: Outlook auto-creates calendar entries during email delivery — stored separately from the email. When the email is deleted, the calendar event persists. .ics file attachments bypass Hard Delete remediation. Safe Links does not inspect QR codes in calendar events.
WHAT CATCHES IT: Pre-delivery inspection of meeting invite content and attached .ics files: decoding QR codes embedded in calendar payloads, evaluating link destinations in Location fields and event bodies, and identifying the social engineering framing used to make the meeting contextually plausible before the entry is ever added to the calendar.
Emerging: The Email-to-Teams Attack Chain
Microsoft's own Defender for Office 365 blog, April 13, 2026, flagged a pattern that every Microsoft 365 security team should be tracking: attackers are increasingly using email as an entry point and Microsoft Teams as the exploitation layer.
The chain works as follows: a phishing email establishes a pretext — an invoice dispute, a contract review, an HR matter — and then directs the target to continue the conversation in Teams, where a 'colleague' is waiting with more information or a document to review. Once the interaction moves to Teams, the social engineering continues in an environment where security awareness is lower, where users are conditioned to trust messages from apparent colleagues, and where many organisations have not extended the same detection coverage they apply to inbound email.
A Russian-linked threat group tracked as Storm-2372 has been documented running this chain against government agencies, NGOs, defence contractors, and critical infrastructure organisations since August 2024, combining Teams-based social engineering with device code phishing to capture authentication tokens without any email-based phishing link at all. The email establishes the relationship. Teams closes the credential compromise.
This is not yet a fully crystallised attack class in the way the eight attacks above are — but the direction of travel is unambiguous. As email security improves, sophisticated actors adapt to the adjacent communication channel where defences are weaker. Security teams evaluating M365 email security in 2026 should ask whether the platform can detect email content engineered to move a conversation to Teams as part of a social engineering chain.
Final Thoughts: The Detection Architecture That Actually Closes These Gaps
Eight attacks. One structural characteristic across all of them: malicious intent, not malicious content. Defender was built to detect malicious content — and it does that extraordinarily well at the commodity threat volume, as the 13 million Tycoon2FA blocks in a single month demonstrate. Against the eight attack types on this list, it produces a clean verdict because it was never designed to inspect the one element that makes these attacks dangerous: their purpose.
At FireEye, every serious email-based incident I investigated had the same pattern. The email that initiated the breach looked technically perfect by every measure we had at the time. The only thing wrong with it was what it was trying to make happen. That observation is what shaped how we designed TRACE at StrongestLayer — around the conviction that the detection architecture has to match the threat architecture. Attacks that carry malicious intent deserve a detection system that reasons about intent.
Adding LLM-native intent reasoning via Microsoft's Graph API does not replace Defender. It adds a second layer that operates on a completely different principle — at the mailbox layer, after delivery, without touching mail flow, without MX record changes, without any disruption to the EOP and Defender stack that handles the content threat volume. The two layers are designed to coexist. Microsoft handles the payload threats. TRACE handles the intent threats. Together they produce the coverage that a Microsoft 365 environment actually needs against the attack types documented in this post.
Microsoft's own December 2025 security documentation acknowledged that Integrated Cloud Email Security solutions 'execute after Microsoft Defender for Office 365 and act as a secondary filter, offering additional detection layers focusing on specific threat types or user behaviour patterns'. The native layer and the intent layer are not competing architectures. They are complementary ones — and the eight attacks on this list are exactly the threat types that the secondary filter exists to catch.
The organisations that manage email security most effectively in 2026 are precise about what their tools detect and what they do not. They know where Defender's coverage ends — and they have closed that gap with a layer that asks a different question. Not 'what does this contain?' but 'what is this trying to accomplish?' — Muhammad Rizwan, CTO, StrongestLayer
Frequently Asked Questions (FAQs)
Q1: Does Microsoft Defender for Office 365 Plan 2 close these detection gaps?
Defender Plan 2 adds important capabilities over Plan 1 and EOP: Threat Explorer, automated investigation and response, attack simulation training, and Priority Account Protection. These are meaningful improvements for SOC teams focused on investigation and response workflows. The detection gaps in this post are architectural rather than tier-based. Zero-payload BEC, compromised vendor accounts, OAuth consent phishing, AI-generated spear phishing, and calendar invite attacks do not produce indicators that content-inspection systems at any subscription tier are designed to detect. Plan 2 enhances your team's ability to investigate and respond to threats. It does not change the fundamental detection model that allows these specific attack types to pass through cleanly.
Q2: Can calendar invite phishing attacks be prevented with Microsoft 365 configuration?
Partially. Mail flow rules can be configured to filter .ics file attachments, and PowerShell can be used to disable automatic processing of external calendar invites at the mailbox level — preventing Outlook from auto-adding meeting requests to calendars. However, Microsoft's own documentation notes that mail flow rules targeting calendar message types only block native Exchange-generated meeting requests, not .ics attachments. And disabling automatic calendar processing affects all external meeting invites, including legitimate ones, creating workflow friction that most organisations find unacceptable at scale. Microsoft's November 2025 Hard Delete update extended remediation to cover calendar entries — but explicitly does not cover entries added via .ics attachments. Configuration reduces exposure; it does not close the gap.
Q3: What is AiTM phishing and why does standard MFA not stop it?
Adversary-in-the-Middle phishing uses a real-time reverse proxy to sit between the user and the legitimate Microsoft 365 authentication server. The user enters credentials and completes an MFA challenge against the genuine Microsoft system — the proxy relays everything in real time. What the attacker captures is the authenticated session cookie issued after successful MFA completion. This cookie grants persistent account access without requiring the credential or MFA code again. Standard MFA — SMS codes, authenticator apps, push notifications — does not protect against this because the MFA challenge is completed genuinely. Only phishing-resistant MFA using FIDO2 hardware security keys is structurally resistant to AiTM, because the cryptographic authentication is bound to the legitimate origin domain and cannot be relayed through a proxy.
Q4: What is OAuth consent phishing and why does it survive password resets?
OAuth consent phishing tricks users into granting a malicious application delegated permission to their Microsoft 365 account through the legitimate Microsoft OAuth consent interface. No credentials are stolen. No MFA is bypassed. The attacker receives an OAuth access token granting persistent API access to email, calendar, OneDrive, and SharePoint — access that survives password resets and MFA re-enrolment because it was granted at the application permission layer, not the authentication layer. Revoking it requires locating and removing the malicious application from Entra ID app registrations. Microsoft's own Security Blog documented active OAuth redirection abuse campaigns in March 2026, with attackers combining this technique with calendar invite (.ics) attachments to increase the legitimacy of the initial phishing email.
Q5: Why does QR code phishing bypass Safe Links in Microsoft 365?
Safe Links works by scanning and rewriting URLs in email bodies at delivery time, then re-checking at click time. QR code phishing embeds the malicious URL inside an image rather than as a hyperlink in the email body — there is no text URL for Safe Links to process. Microsoft's own Defender documentation explicitly states that 'Safe Links only inspects clickable URLs and does not protect against QR codes.' When the user scans the QR code with a personal mobile device, the URL is decoded by the camera app and opened in the mobile browser — bypassing Safe Links, bypassing corporate web filtering (which only covers managed devices on managed networks), and bypassing conditional access policies requiring compliant devices.
Q6: How does an API-native email security platform work alongside Microsoft Defender without conflicts?
API-native platforms connect to Microsoft 365 through the Microsoft Graph API at the mailbox layer — after Defender and EOP have already processed the message and delivered it. There is no MX record change, no mail flow reconfiguration, and no requirement to disable any Microsoft protection. The platform reads delivered mailbox content through the Graph API, applies its own analysis, and takes action (quarantine, flag, alert) without touching the delivery pipeline. Defender processes inbound mail flow for content threats. The API-native platform processes delivered mailbox content for intent threats. Microsoft's own documentation describes this as Integrated Cloud Email Security — a complementary secondary filter layer that executes after Defender and addresses threat types that content-inspection systems are not designed to detect.
Q7: How long does deploying AI-native email security for Microsoft 365 take?
With Graph API integration, deployment is measured in hours. The process involves creating a service account or app registration in the Microsoft 365 tenant, granting the required Graph API read and action permissions, and completing the platform configuration. Most API-native platforms reach active monitoring of the full production mailbox environment within 24 hours of tenant connection — without MX record changes, mail flow reconfiguration, or any period of reduced protection. This contrasts with gateway-based deployments requiring MX record changes, which typically require four to eight weeks of phased migration to reach full production coverage without disrupting mail delivery.
Sources
Permiso Security: CVE-2026-26133 — Cross-Prompt Injection in Microsoft Copilot (March 2026)
OWASP: LLM01:2025 Prompt Injection — Top 10 for Large Language Model Applications 2025
FBI Internet Crime Complaint Center: 2024 Internet Crime Report
IBM: Cost of a Data Breach Report 2025
Verizon: 2025 Data Breach Investigations Report
Subscribe to Our Newsletters!
Be the first to get exclusive offers and the latest news
Your gateway can't see
what's already inside.
Deploy in minutes, not months. Zero tuning. See what your current tools are missing.






