Evolution of Email Security: Why the "Gateway" Era Architecture Can't Survive the API Future

If you were a Chief Information Security Officer (CISO) in 2015, your email security strategy was simple: Build a moat.
You bought a Secure Email Gateway (SEG)—likely Mimecast. You pointed your MX records to their cloud, and they acted as the ultimate bouncer. Every single email that tried to enter your organization had to pass through their scanners first. If it contained a known virus, it was blocked. If it contained a known bad link, it was rewritten.
For a decade, this "Castle and Moat" architecture was the gold standard. It was elegant, effective, and necessary.
But the world has changed.
Today, we no longer live in castles. We live in the cloud (Microsoft 365, Google Workspace). And the enemies we face in 2026—AI-driven Business Email Compromise (BEC), internal account takeovers, and supply chain fraud—do not attack the moat. They simply walk across the drawbridge using valid credentials.
This article is not a critique of the companies that built the Gateway era. Mimecast is an engineering marvel. But it is an analysis of why the Gateway Architecture itself is fundamentally unsuited for the threat landscape of the AI era—and why the industry is inevitably shifting toward API-Integrated Cloud Email Security (ICES).
Why are Gateways Struggling? (Packet vs. Context)
To understand why Gateways are struggling, we must look at the code level.
The "Mailman" Problem
A Secure Email Gateway (SEG) functions as a Mail Transfer Agent (MTA). It sits in front of your email server.
When an email arrives, the SEG has milliseconds to make a decision: Allow or Block.
To make this decision, it looks at the Packet:
- The Header: Is the IP address on a blacklist?
- The Payload: Does the attachment hash match a known virus?
- The Link: Does the URL lead to a known phishing site?
If the packet looks clean, the SEG stamps it "Safe" and passes it to Microsoft 365. Once that handover happens, the SEG is blind. It cannot see what happens next.
The AI Reality
The problem is that modern AI attacks do not have malicious packets.
- BEC attacks are pure text. There is no malware to scan.
- QR Code Phishing (Quishing) moves the attack off-network to a mobile device.
- Supply Chain Attacks come from valid, whitelisted vendor accounts that have been compromised.
According to our Three Axes of Email Security framework, AI-generated threats show only 5-15% Jaccard similarity to historical patterns. This means 85% of modern attacks look completely unique to a legacy scanner.
The SEG looks at a BEC email from a compromised vendor and sees: "Valid IP, Valid SPF/DKIM, No Malware, No Links." It lets the email through because it is looking for a "Bad Thing" (Payload) instead of "Bad Intent" (Behavior).
The Takeaway: You cannot patch a Gateway to understand human intent. That is an architectural limitation, not a feature bug.
Why does the Gateway miss internal threats? (East-West Traffic)
If there is one reason why CISOs are moving away from the pure Gateway model, it is this: Lateral Movement.
The Journaling Nightmare
Gateways are designed for North-South traffic (Inbound from the internet / Outbound to the internet). They are natively blind to East-West traffic (Internal-to-Internal).
If an attacker compromises an employee's account and uses it to email the CEO, that email never leaves your Microsoft 365 tenant. It never hits the MX record. The Gateway never sees it.
Legacy providers like Mimecast try to fix this with "Journaling."
- You configure Microsoft Exchange to send a copy (Journal) of every internal email out to the Mimecast cloud.
- Mimecast scans the copy.
- If it finds a threat, it tries to reach back into Microsoft 365 and delete the original.
Why this fails in 2026:
- Latency: By the time the copy is scanned and the remediation signal is sent, the user has often already clicked.
- Complexity: Journaling rules are notoriously fragile and difficult to configure.
- Cost: You are paying to duplicate and store massive amounts of internal traffic.
The API Advantage
StrongestLayer (and other API-native tools) takes a fundamentally different approach. We do not sit at the perimeter. We sit inside the API.
We treat Internal email exactly the same as External email. Because we are integrated directly into the Microsoft Graph API, we see the internal threat in real-time, without the need for complex journaling rules.
The "Zombie Rules" Problem (Complexity as a Vulnerability)
Security is only as good as its configuration. And here lies the paradox of the Gateway: Granularity is a liability.
The 1,000-Knob Problem
Legacy tools sell themselves on "Control." They give you 1,000 knobs to turn.
- Block this domain.
- Allow this sender.
- Rewrite this URL unless...
- Quarantine if spam score is > 5.
In 2015, sysadmins loved this. In 2026, it creates "Zombie Rules."
These are dormant configurations—often 40-50% of your total ruleset—that sit forgotten in the background. You create an exception for the Marketing team on Tuesday, and six months later, that exception is the hole an attacker walks through.
The Shift to Autonomy
The future of security is Autonomous.
At StrongestLayer, we believe humans should not be writing the rules. The AI should learn the baseline and write the rules itself.
- Legacy Model: Admin manually updates a blocklist when a new threat appears (Reactive).
- StrongestLayer Model: The AI notices a deviation in tone and relationship strength and flags the email automatically (Proactive).
We don't give you knobs. We give you answers.
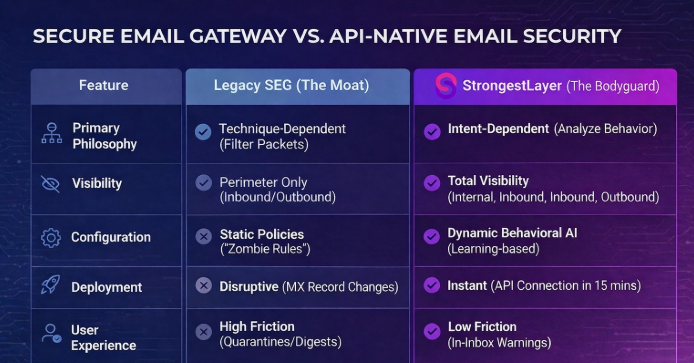
Technique-Dependent vs. Intent-Dependent (The Gap Analysis)
We often hear the question: "Should I rip out Mimecast?"
For many organizations, the answer is No.
Mimecast is still an excellent "Moat." It is fantastic at bulk spam filtering, archiving, and compliance. But it is no longer sufficient as a standalone defense because it is Technique-Dependent. It relies on identifying known bad signatures.
StrongestLayer is Intent-Dependent. We analyze the "why" behind the email, not just the "what."
Here is where the "Gap" exists—and how an API layer fills it.
Final Thoughts (The Hybrid Future)
The cybersecurity industry is notorious for "Rip and Replace" marketing. New vendors claim old vendors are dead.
We disagree.
The Gateway is not dead. But its role has changed.
- In 2015: The Gateway was the Whole Strategy.
- In 2026: The Gateway is the Filter Layer.
The modern, resilient security stack is Hybrid.
- Layer 1 (The Filter): Use Microsoft 365 Native Security or a Legacy SEG (Mimecast) to block the billions of spam messages and known viruses. Let them do the heavy lifting.
- Layer 2 (The Intelligence): Use StrongestLayer inside the API to catch the 1% of attacks that actually matter—the AI-driven, socially engineered threats that slip past the filter.
Do not leave the castle unguarded from the inside.
Technical FAQ: Mimecast vs. StrongestLayer
Q1: Can I run StrongestLayer and Mimecast at the same time?
Yes. In fact, this is a common deployment. Mimecast handles the perimeter hygiene, and StrongestLayer provides the internal visibility and anti-fraud intelligence that Mimecast lacks.
Q2: Mimecast claims they have "Internal Email Protect" (IEP). Isn't that the same?
No. Mimecast’s IEP relies on Journaling, which involves sending copies of internal emails out to their cloud. It introduces latency and complexity. StrongestLayer is API-Native, meaning we live inside the Microsoft 365 environment, offering faster, native detection without traffic duplication.
Q3: Does StrongestLayer require changing my MX records?
Never. We connect via the Microsoft Graph API. You can deploy us in 15 minutes without disrupting your mail flow. This also means if our service ever goes down (which it won't), your email keeps flowing. If a Gateway goes down, your email stops.
Q4: Mimecast has "CyberGraph" AI. How is StrongestLayer different?
CyberGraph is an add-on that attempts to add intelligence to the Gateway. However, it is still fundamentally limited by its position at the perimeter. StrongestLayer’s AI is built on Behavioral Baselines (who talks to whom, how, and when), allowing us to detect subtle anomalies in relationship patterns that rule-based AI misses.
Subscribe to Our Newsletters!
Be the first to get exclusive offers and the latest news
Your gateway can't see
what's already inside.
Deploy in minutes, not months. Zero tuning. See what your current tools are missing.





